12 Cybersecurity Tools on Linux That Will Keep Your System Secure
Here are 12 Cybersecurity Tools on Linux That Will Keep Your System Secure — Don’t Be the Next Target!

Here are 12 Cybersecurity Tools on Linux That Will Keep Your System Secure — Don’t Be the Next Target!
Introduction
Linux is a powerful and versatile operating system that is widely used by developers and power users alike. Despite its reputation for being secure, Linux is not immune to security threats. In fact, there are a number of security risks that come with using Linux.
Fortunately, there are a number of tools that can help you secure your Linux system. In this article, we will take a look at 10 of the best cybersecurity tools for Linux.
- Firewall
A firewall is a critical tool for security. It can help you block incoming traffic that could be harmful to your system. There are a number of different firewalls available for Linux, such as iptables, firewalld, and ufw.
2. SELinux
SELinux is a security feature that is built into the Linux kernel. It provides a way to control access to files and resources on your system. SELinux can be used to improve the security of your system by preventing unauthorized access to sensitive files.
3. AppArmor
AppArmor is another security feature that is built into the Linux kernel. It provides a way to control the permissions of programs on your system. AppArmor can be used to improve the security of your system by preventing programs from accessing files that they should not have access to.
4. GnuPG
GnuPG is a tool that can be used to encrypt and sign data. It can be used to protect your privacy by encrypting your email messages and files. GnuPG can also be used to verify the authenticity of signed documents.
5. SSH
SSH is a tool that can be used to securely connect to another computer. It can be used to remotely access a system or to transfer files between computers. SSH can also be used to tunnel traffic through a network.
6. VPN
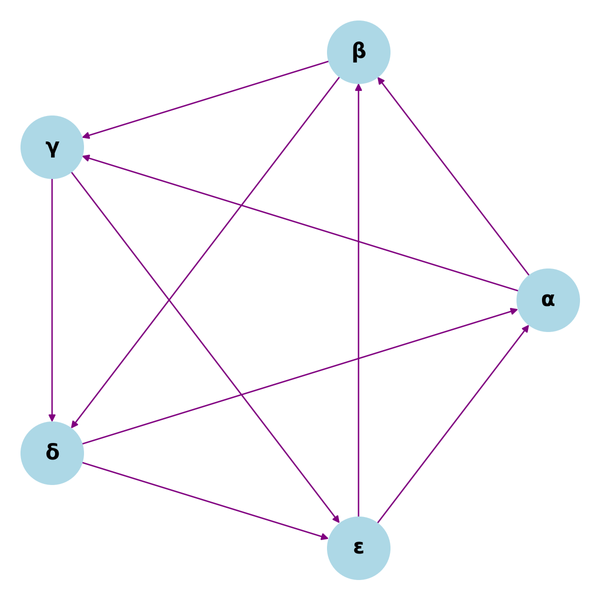
A VPN is a tool that can be used to securely connect to another network. A VPN can be used to connect to a private network or to the internet. A VPN can also be used to bypass firewalls or to encrypt your traffic. Some of the popular VPN Protocols are WireGuard, IPSec, and OpenVPN.
7. Tor
Tor is a tool that can be used to anonymously browse the internet. Tor encrypts your traffic and routes it through a network of computers, making it difficult to track your activity.
8. Rkhunter
Rkhunter is a tool that can be used to scan your system for rootkits. Rootkits are a type of malware that can be used to gain unauthorized access to a system. Rkhunter can help you detect and remove rootkits from your system.
9. Lynis
Lynis is an open-source security auditing tool. It can be used to scan your system for vulnerabilities and to report on the security of your system. Lynis can help you to harden your system and to improve its security.
10. Chkrootkit
Chkrootkit is a tool that can be used to scan your system for rootkits. Rootkits are a type of malware that can be used to gain unauthorized access to a system. Chkrootkit can help you detect and remove rootkits from your system.
11. Tripwire
Tripwire is a tool that can be used to monitor your system for changes. Tripwire can be used to detect changes to files, configurations, and installed programs. Tripwire can help you to detect and investigate potential security breaches.
12. Ossim
Ossim is a tool that can be used to monitor and manage your security data. Ossim can be used to collect data from a variety of security devices, such as intrusion detection systems and firewalls. Ossim can help you to detect and respond to security incidents.
“If you want to learn Linux, but don’t know where to start, Sign up for my upcoming eBook - Linux for Beginners: The Terminal Made Easy, for a chance to learn the basics of Linux and about this amazing open-source operating system that is taking the world by storm! Get a 35% Discount by Signing up now!”. Use this link:
Check out my Website — Narasimman Tech for Tutorials, Tips, Resources, and more. Sign up for my Weekly Newsletter to get Premium articles for free!
Follow me on Twitter for quick tips!